EIP-7702 Batch Approval Scams and Prevention Guide
EIP-7702 Batch Approval Scam Full Analysis: How One Signature Can Drain Your Wallet
EIP-7702 is a core feature of Ethereum’s Pectra upgrade. It was designed to bring Account Abstraction to regular wallets, enabling gas payment in stablecoin, batch transactions, and other conveniences. However, since its launch, it has quickly become a new tool for scammers. Multiple million-dollar theft incidents in 2025 were related to it. A single mistaken signature can result in your assets being wiped out instantly.
This article breaks down the principles of EIP-7702, common scam tactics, a real EIP-7702 authorization theft case, and practical prevention methods to help you improve wallet security while using this technology safely.
Part 1: What is EIP-7702?
Traditional Ethereum accounts are mainly divided into two types:
- EOA (Externally Owned Account): Regular wallet addresses we use daily, controlled only by private keys. They cannot execute complex logic or batch operations and must pay gas fees themselves.
- Smart Contract Account: Powerful, capable of batch operations and permission control, but requires address migration.
EIP-7702 solves the limitation that EOAs cannot perform batch transfers. It allows regular EOAs to temporarily borrow smart contract code through a single signature authorization during a transaction, enabling batch transfers and gas payment in stablecoin without changing the original address.
Core Technical Structure:
- Adds an
authorization_listfield containing authorization tuples (chain_id, delegate_address, nonce) and user signature. - During execution, the EVM temporarily injects the delegate contract code into the EOA (delegation designator: 0xef0100 || address) and automatically removes it after execution.
- Combined with ERC-4337, it supports EntryPoint, Bundler, and Paymaster to enable gas payment in stablecoin and batch transactions.
In one sentence: EIP-7702 turns your old wallet into a “smart account” instantly, greatly improving user experience, but it also opens new security risk windows.
Part 2: EIP-7702 Scam Case Analysis
2.1 Summary of Common EIP-7702 Scam Tactics
After EIP-7702 went live, scam groups (such as Inferno Drainer and Pink Drainer) quickly adapted, leveraging its “one authorization = persistent execution rights” feature to upgrade traditional multi-step phishing into highly efficient and stealthy attacks.
According to security agencies, during certain periods over 80%-97% of EIP-7702 authorizations flowed to malicious contracts, with many single incidents resulting in million-dollar losses. These attacks are extremely deceptive, and users often mistake them for “normal Bundler execution” or “official features.”
Main Scam Tactics:
- Fake Websites / Fake Wallets / Fake Airdrops: Using fake sites, fake wallets, or fake airdrop links to offer “wallet upgrade to smart account,” “claim airdrop rewards,” or “gas payment verification,” tricking users into signing malicious EIP-7702 authorization contracts.
- Fake DApp / Fake Trading Interfaces: Imitating popular platforms like Uniswap, displaying seemingly normal “batch Swap” or “Approve” signatures that actually install malicious Delegator contracts.
- Batch Execution Trap: Combined with ERC-4337, a single signature completes multiple malicious operations, instantly draining user assets.
- Combined with Private Key Leak: First obtain the private key through viruses or phishing, then use EIP-7702 to install a “sweeper” contract for low-fee batch theft.
2.2 Real Case Analysis: Complete Attack Process of EIP-7702 Authorization Theft
The following uses a specific victim case as an example to demonstrate a typical EIP-7702 + ERC-4337 combined attack.
Attack Steps Breakdown:
-
Inducement and Signing Stage
The user clicks on a fake DApp, airdrop link, or Telegram “upgrade to claim rewards” bait. The wallet pops up a signature request that appears to be a normal batch transaction or gas payment in stablecoin, but is actually a malicious EIP-7702 authorization (delegating to a malicious contract, usually a batch execution contract). -
Authorization Installation Stage
After the user confirms the signature, the malicious batch execution contract is “installed” into the EOA address, granting the attacker persistent batch execution rights. No further signatures or private keys are needed afterward. -
Remote Theft Stage
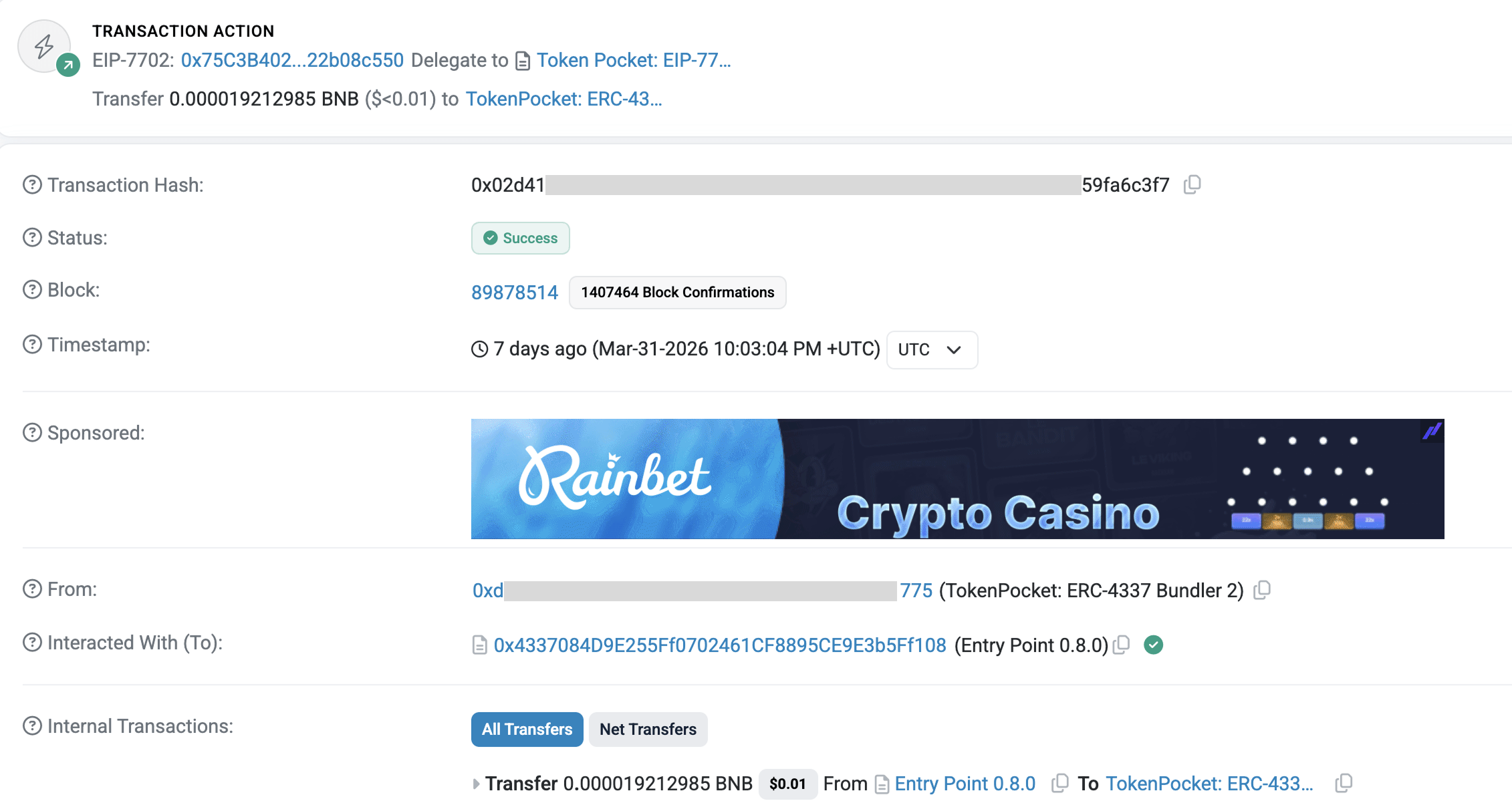
The attacker submits batch operations through a Bundler (displayed as TokenPocket: ERC-4337 Bundler 2, which users often mistake for an official TokenPocket address).
It triggers the EntryPoint contract to execute the batch, directly transferring the victim’s token assets.
Gas fees are extremely low (about 0.000017 BNB ≈ $0.01), paid by the attacker or Bundler (reverse use of the sponsorship feature). The funds are then sent to mixing addresses. -
Subsequent Exploitation
Once the authorization takes effect, the attacker can trigger it multiple times remotely until the user transfers the remaining assets.
Key Lesson: The entire process requires no private key leak. One mistaken signature can lead to the account being remotely “taken over.” This is exactly how EIP-7702 upgrades traditional phishing into “invisible hijacking.”
Part 3: How to Prevent EIP-7702 Scams?
Most Important Principle: Understand before signing — trust only official channels.
Daily Prevention Measures:
- Reject “upgrade,” “batch confirmation,” “gas payment in stablecoin,” or “wallet verification” signatures from unknown websites, especially when delegation, set code, or batch execute fields appear.
- Only connect DApps within official wallet apps and avoid clicking external links.
- Carefully check the wallet popup content and target contract address before signing. If unsure, reject it.
- Test new features with small amounts first.
- If anything unusual occurs, immediately transfer remaining assets to a new clean address (hardware wallet recommended).
- Regularly use tools like revoke.cash or TokenPocket’s risk authorization management tool to check and revoke suspicious EIP-7702 authorizations.
TokenPocket is one of the earliest mainstream wallets to fully support EIP-7702. It has built-in risk authorization detection and one-click management features. Users can intuitively view the list of authorized Delegators in the App, quickly identify high-risk contracts, and revoke them. It is recommended to update to the latest version and prioritize using official TokenPocket channels for related operations to significantly reduce the risk of mistaken signatures.
FAQs about EIP-7702
1.EIP-7702 Standards and Implementation
EIP-7702 is a new transaction type (0x04, Set Code Transaction) in Ethereum’s Pectra upgrade. It allows externally owned accounts to temporarily delegate execution rights to smart contracts via a user-signed authorization list. The Ethereum Virtual Machine injects the delegate code during transaction execution and removes it afterward, enabling regular accounts to gain smart account features without changing their address.
2.How Does EIP-7702 Compare To Other Ethereum Improvement Proposals?
EIP-7702 is a core protocol upgrade for Ethereum. It allows regular externally owned accounts to temporarily gain smart contract execution capabilities without changing their original address. Compared to other account abstraction solutions, it provides more direct protocol-level support for smart accounts, achieving better compatibility and security.
3.Can You Explain The Main Benefits Of EIP-7702 For Developers?
EIP-7702 allows developers to add smart account features (such as batch transactions, gas payment in stablecoin, session keys, and permission controls) to existing externally owned accounts without requiring users to migrate addresses or redeploy contracts. It simplifies user experience improvements, reduces gas costs for complex operations, and makes it easier to integrate advanced wallet logic while preserving the user’s original address.
Conclusion
EIP-7702 brings revolutionary conveniences such as gas payment in stablecoin and batch transactions, significantly improving the experience for regular users. However, the design of “one authorization grants persistent execution rights” also makes scam attacks more efficient and stealthy.
While enjoying the benefits of the technology, security awareness is always the first line of defense: develop the habit of “understand the signature before confirming,” use only official TokenPocket channels to download wallets, and regularly check authorizations. Protecting every click means protecting your crypto assets. If you encounter suspicious signatures or have suffered similar losses, revoke the authorization and transfer assets immediately. You can also refer to the latest reports from GoPlus Security and SlowMist for more information.
Disclaimer
Cryptocurrency investment and usage involve market, legal, and technical risks. Please operate with caution. Always keep your mnemonic phrases and private keys safe and never share them with anyone. This article is for reference only and does not constitute investment advice. Before using any wallet, please conduct your own research and ensure compliance with local laws and regulations.